RouteReceipts for Stripe: Security, Permissions, and Compliance FAQ (App Scopes, Data Flows, GDPR/SOC 2, Audit Evidence)

RouteReceipts for Stripe: Security, Permissions, and Compliance FAQ (App Scopes, Data Flows, GDPR/SOC 2, Audit Evidence)
A misaligned app scope in Stripe can force security teams to delay procurement by days. RouteReceipts Stripe app permissions and scopes is a breakdown of the specific Stripe OAuth scopes, webhook events, and read/write actions that Route Receipts requests, showing what data flows and why. This FAQ-based article explains what Route Receipts stores, how the allowlist controls invoice delivery inside the Stripe dashboard, where decision audit logs live, and which documents security reviewers should request. See our RouteReceipts Stripe setup guide for installation and scope mapping, consult our RouteReceipts privacy policy for data handling, and check our RouteReceipts Stripe receipt routing FAQ. Route Receipts offers a free plan with 20 receipts. Which audit artifacts will satisfy your procurement checklist?
What are the key RouteReceipts Stripe app permissions and scopes?
Route Receipts requests a focused set of Stripe scopes that let the app read customer contact fields, inspect charge and invoice events, and record receipt-routing decisions. These scopes are the minimum required to evaluate whether a receipt should be sent, to maintain an allowlist, and to write decision audit entries for transparency. Reviewing these permissions during procurement ensures teams avoid unnecessary broad access.
Which Stripe scopes does Route Receipts request? 🛠️
Route Receipts requests read access to customer contact data, read access to charge and invoice events, and write access limited to routing decisions and allowlist records. Route Receipts reads customer email and phone fields to confirm allowlist membership and reads charge or invoice events to detect when a receipt would be generated. The app then writes a routing decision (stored in the Route Receipts decision audit log) and, when configured, can suppress Stripe's automatic receipt for that transaction.
Route Receipts documentation lists exact scope names and the install consent language; procurement teams should compare that text to their security policy. See our Route Receipts documentation for the install checklist and consent wording.
How do connected-account scopes differ from platform-level scopes? 🔐
Connected-account scopes limit Route Receipts to a single Stripe account, while platform-level scopes permit access across multiple connected accounts. For businesses using Stripe Connect, choosing account-scoped installs reduces blast radius and keeps audit trails per account. Route Receipts requests per-account consent when installed on a connected account and logs the decision for each account separately to simplify audits.
Use Stripe's Entitlements API and the Route Receipts decision log to verify which accounts granted which scopes after install. That lets procurement revoke or narrow access without pulling engineering into a long remediation project.
⚠️ Warning: Prefer account-scoped installs for enterprise customers where possible; platform-level write permissions increase compliance review time and require stricter data retention controls.
Permissions comparison table 📊
| Scope (business level) | What Route Receipts does with it | Account-scoped or object-scoped | Procurement risk and mitigation |
|---|---|---|---|
| Read customer contact fields (example: customers.read) | Reads email/phone to determine allowlist membership and preferred delivery | Typically account-scoped | Low risk if limited to contact fields; require admin consent and periodic review via Route Receipts documentation and audit log |
| Read charges and invoices (example: charges.read, invoices.read) | Detects invoice or charge events that would trigger a Stripe receipt | Account-scoped | Medium risk for transaction visibility; mitigate by approving only required event types and reviewing event retention in our Privacy Policy (see Stripe app data retention GDPR) |
| Manage allowlist entries and routing decisions (example: app-specific write) | Creates and updates allowlist records and writes decision audit entries in the Route Receipts dashboard | Object-scoped to app-managed records | Medium risk if write scope expands; require granular admin permissions, require audit-log export during procurement review |
| Suppress automatic receipts or toggle invoice settings (example: invoices.update) | Optionally suppresses Stripe's automatic email for specific transactions to avoid duplicates | Account-scoped and higher privilege | Higher risk because it changes customer-facing behavior; require explicit admin approval, test installs on a staging account, and document rollback steps |
| Data retention metadata (no direct Stripe scope) | Route Receipts stores decision logs and allowlist entries according to our retention policy | N/A (product-level) | Review Route Receipts privacy policy for retention periods and GDPR handling; include retention clauses in procurement contract |
Each scope row above maps a business action to the practical control and suggested mitigation steps. Procurement teams should cross-check the exact scope tokens on our install screen against the table and use the Route Receipts documentation when preparing an approval packet.
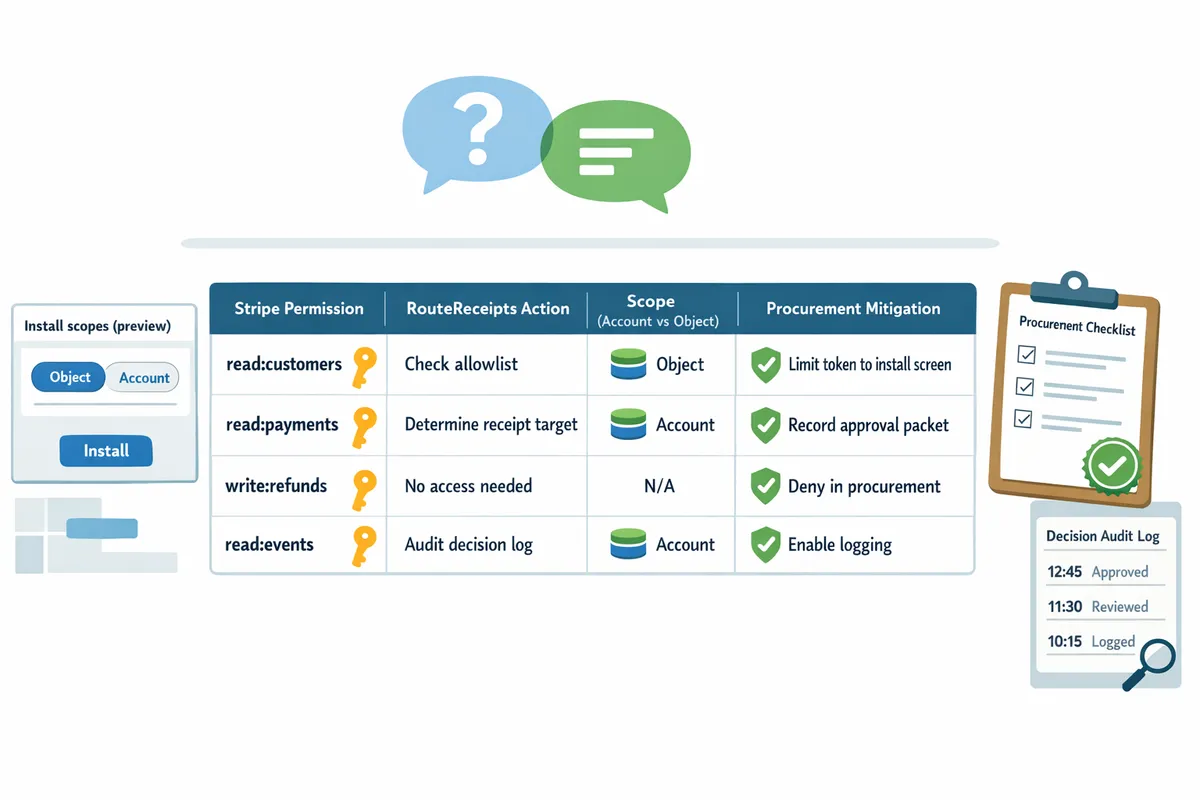
For questions about installing on a production versus staging account, see our installation guide in the Route Receipts documentation and consult the Route Receipts FAQ for common procurement concerns. If you need a permissions audit or to revoke access post-install, contact Route Receipts support for a step-by-step checklist and exportable audit evidence.
How do RouteReceipts permissions map to concrete receipt-routing tasks and business risk?
Route Receipts maps specific Stripe scopes to discrete receipt-routing tasks so reviewers can see which permission enables each action. This mapping reduces ambiguity for procurement, security, and SOC 2 reviewers by showing exactly what Route Receipts can read or change in your Stripe account. Below you will find a scoped permissions table, short Q&A on common tasks, and a post-install audit checklist that reviewers can use during procurement.
| Stripe scope (example) | Route Receipts task | Operational impact | Quick mitigation checklist |
|---|---|---|---|
| customers.read | Look up customer contact fields and metadata to evaluate allowlist status | Allows Route Receipts to decide whether a customer should receive a receipt | Grant read-only where possible; enable decision audit log; document retention in the privacy policy |
| customers.write | Set allowlist flag on a customer record or update customer metadata | Lets Route Receipts add or remove customers from the allowlist without developer work | Limit write to the minimum account; require install approvals; use periodic permission reviews |
| invoices.read, charges.read, events.read | Inspect invoice.paid or charge.succeeded events to evaluate routing decisions | Provides the event stream Route Receipts uses to determine send/suppress actions | Use least privilege; test on a staging account; confirm webhook signing and event filters |
| invoices.write or charges.write | Suppress or trigger a receipt send after a routing decision | Enables Route Receipts to block Stripe automatic sends or programmatically resend receipts | Disable Stripe automatic receipts per docs; audit sends; require change management approval |
| metadata.write (customer or invoice) | Record routing decisions and link to the decision audit log | Creates auditable evidence tied to objects for compliance reviewers | Retain audit logs; limit retention window; surface logs in the dashboard |
Which permission enables allowlist creation and editing? ✍️
Allowlist creation and editing require both customer read access and customer write permission so Route Receipts can check contact fields and then mark the customer as allowlisted. Route Receipts stores the allowlist status in a customer-level flag or metadata field and documents this flow in the setup guide. For example, adding customer@example.com to the allowlist updates that customer's metadata so future invoice events are routed according to the flag. Security teams should grant write scope only during initial setup and follow the post-install audit steps in our Documentation to verify expected behavior. See the RouteReceipts FAQ for common installation questions and the step-by-step setup in our Documentation.
💡 Tip: Enable the Route Receipts decision audit log before granting write scopes so every allowlist change is recorded and traceable.
What permission controls sending or suppressing receipts? ✉️
Receipt suppression and programmatic sending require read access to invoice or charge events plus a write permission that lets Route Receipts block or trigger sends. Route Receipts evaluates events such as invoice.paid or charge.succeeded, checks the allowlist, and then either prevents Stripe from emailing the receipt or instructs Stripe to send it for allowlisted customers. For example, Route Receipts will suppress Stripe's automatic receipt when an invoice arrives for a non-allowlisted customer and will trigger a resend when a customer is on the allowlist. Follow the Documentation to disable Stripe automatic receipts during setup so you avoid duplicate emails. Test the flow on a staging Stripe account and include the decision log when presenting evidence to SOC 2 reviewers.
What are the business risks of granting broader scopes and what controls reduce that risk? ✅
Broader scopes increase exposure to customer data and widen the blast radius of configuration errors. Granting unnecessary read or write access can let an app view payment details or modify customer records, which raises data protection and change-management concerns for procurement and SOC 2 reviewers. Map each granted scope to a business need, keep a record of who approved the install, and enforce periodic reviews.
Common risks and controls:
- Excessive data access. Limit to resource-level scopes such as customers.read instead of account-wide read. Document decisions in procurement notes.
- Unintended writes. Restrict customers.write and invoices.write to the minimum accounts and enable the decision audit log for every write action.
- Retention and GDPR exposure. Document data retention settings and delete or anonymize routing metadata per our Privacy Policy. This ties to Stripe app data retention GDPR requirements.
- Change-management gaps. Require a formal install approval, add the app to an allowlist of approved integrations, and schedule quarterly permission reviews.
Post-install audit and permission revocation workflow:
- Verify granted scopes match the minimal list in the setup guide. See our Documentation for the recommended scope set.
- Confirm Route Receipts has updated a test customer's allowlist flag and that the change appears in the decision audit log.
- Run a simulated invoice.paid event in staging and confirm suppression or resend behavior.
- Check that Stripe automatic receipts were disabled to avoid duplicates.
- Log the installation in procurement records and schedule the next permission review.
SOC 2 reviewers can map these steps to access control and change management controls by attaching the decision audit log and procurement approval as audit evidence. If you need help during the review, contact Route Receipts support or consult the FAQ and setup guide for example artifacts.
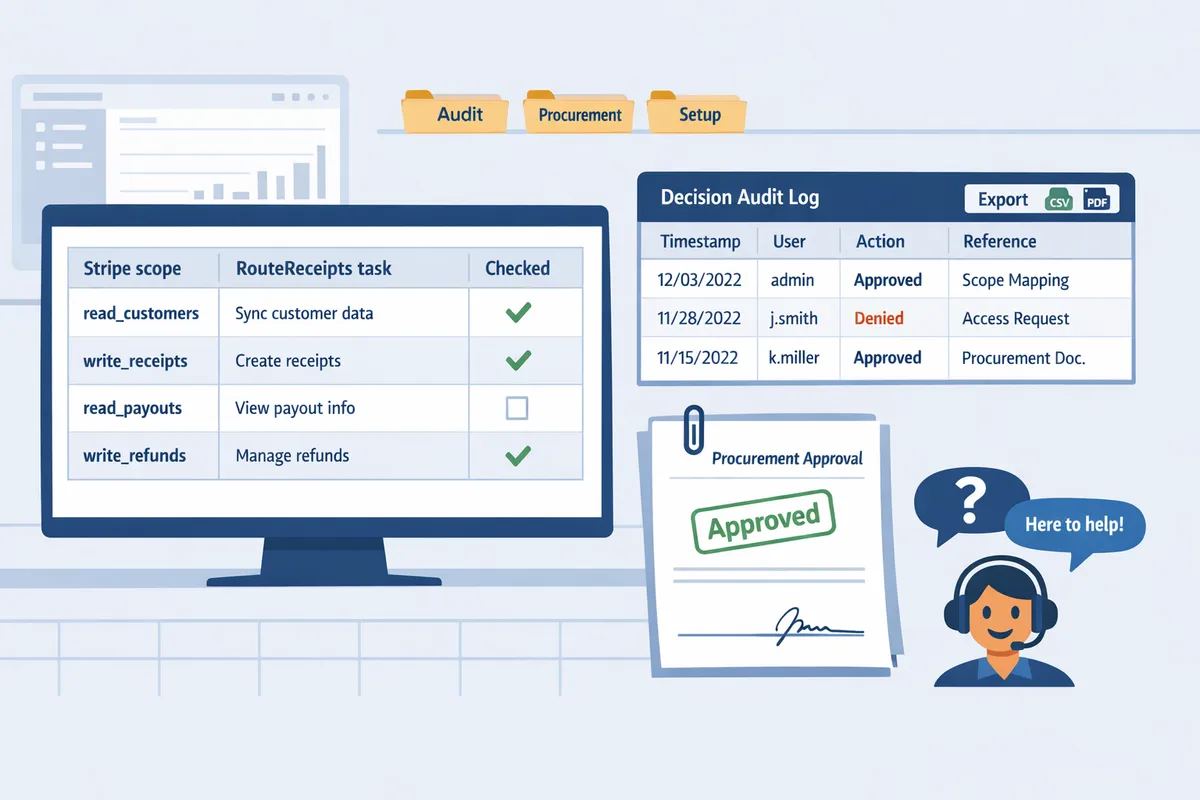
How do I audit, revoke, and gather compliance evidence for RouteReceipts after installation?
Perform a focused post-install audit: confirm the granted Stripe scopes, export Route Receipts' decision audit log for the review period, and document data retention and processing for GDPR and SOC 2 reviewers. Route Receipts provides a dashboard-native decision log and references its data practices in our privacy policy to support evidence collection. Follow a repeatable workflow so procurement, security, and auditors can reproduce the same artifacts.
What is the step-by-step post-install permissions audit? 🔎
List installed scopes in the Stripe dashboard, export Route Receipts' decision audit log for your review window, and validate routing behavior in a staging account before changing production settings.
- Open your Stripe account and go to Settings > Connected apps > Route Receipts to save the installed-scope listing as a PDF or screenshot for auditors.
- From our dashboard, export the decision audit log for the review period (example: last 90 days). See the Route Receipts documentation for export instructions.
- Disable Stripe's automatic receipts in a staging Stripe account to prevent duplicates, then replay a representative set of invoice/charge events to confirm routing decisions match the allowlist.
- Timestamp and hash each exported artifact in your evidence folder so auditors can verify integrity.
- Record who performed the audit, when, and the test cases used (customer IDs, invoice numbers).
Route Receipts surfaces decision entries and test-mode behavior in the dashboard so you can prove the exact actions taken during the audit.
What artifacts should I collect for SOC 2 and GDPR requests? 🧾
Collect the Stripe-installed-scope listing, Route Receipts' decision log exports, and our privacy policy and retention schedule as the core compliance pack.
- Installed-scope export shows least-privilege and who granted access.
- Decision audit log shows every routing decision with timestamp, trigger (invoice/charge), and reviewer or system action.
- Privacy policy and retention documentation show what personal fields we store and for how long; reference our privacy policy for the canonical text.
- Support tickets or change requests that authorized scope changes or retention exceptions.
Use the table below to map artifacts to common audit needs.
| Artifact | What it proves | Where to get it |
|---|---|---|
| Installed scopes (Stripe) | Shows exactly which permissions Route Receipts holds and who approved them | Stripe dashboard (Connected apps) |
| Decision audit log export | Demonstrates authorized routing actions with timestamps for SOC 2 logging and GDPR access requests | Route Receipts dashboard export (see Documentation) |
| Privacy policy and retention schedule | Explains data types, retention periods, and deletion processes for GDPR review | Our privacy policy page |
| Change/approval records | Evidence of least-privilege reviews and who signed off on permission changes | Internal change control system or support request threads |
Map each artifact to the SOC 2 control category being assessed: access controls (installed scopes), logging and monitoring (audit log), and data retention and deletion (privacy policy). For GDPR subject access or deletion requests, export the decision log entries for the requested customer ID and record the deletion timestamp and method.
How do I revoke or reduce permissions without disrupting receipts? ⛔
Reduce app scopes in Stripe and iterate changes in a staging account while watching Route Receipts' decision log and dashboard for missing-permission errors.
- Identify the minimal scope set required for routing (example mapping below).
- Make the change first in a staging Stripe account and run the same set of invoices/charges used in your audit.
- Monitor the Route Receipts decision log and dashboard for immediate errors; Route Receipts surfaces missing-permission alerts so you know which action failed.
- If routing fails, restore the previous scope, document the failure mode, and adjust the scope reduction plan.
- Once staging passes, schedule a maintenance window to apply the same change in production and repeat the test cases.
💡 Tip: Always test scope reductions in a staging account with real sample invoices before changing production.
Use the example mapping below to understand business impact before revoking permissions.
| Permission (business form) | What it enables in Route Receipts | Business impact if removed |
|---|---|---|
| Read customer contact fields | Match allowlist entries (email or customer ID) to decide who receives receipts | Allowlist matching fails; receipts may be sent to default recipients or blocked incorrectly |
| Read invoices/charges | Inspect invoice metadata and decide routing at the time of issuance | Routing decisions cannot run; receipts may go to all or none depending on Stripe settings |
| Write routing flags / decision records | Record that a receipt was routed or suppressed for audit | Loss of auditable decision entries; harder to demonstrate authorized actions to auditors |
For hands-on steps, follow our Route Receipts documentation and contact Support if a scope reduction causes unexpected behavior. If auditors request evidence of scope changes, include the installed-scope export, the decision log segment that covers the change window, and the approval record for the change.
Related reading: our Frequently Asked Questions covers install and allowlist basics, and the Route Receipts documentation provides step-by-step export and test instructions. For help with a live issue, contact our support page.
Frequently Asked Questions
This FAQ answers operational, security, and compliance questions procurement and security reviewers ask about Route Receipts' Stripe integration. It points to concrete next steps, the Route Receipts privacy policy, and our setup documentation so teams can gather audit evidence quickly.
Which Stripe scopes does Route Receipts actually need? 🤔
Route Receipts requests a minimal set of Stripe scopes needed to read customer contact fields, inspect invoice and charge events, and record routing decisions. Our documentation lists the exact install consent language and the precise scope names; refer to the Route Receipts Stripe setup guide for the canonical list. At a high level, those scopes map to three actions: reading customer records (to find emails or customer IDs), reading invoice/charge events (to determine when to consider sending a receipt), and writing lightweight metadata or decision records (to mark that a receipt was allowed or suppressed). For procurement reviews, capture the install consent screen and compare each requested scope to this action mapping to confirm least privilege. See our Documentation for the full mapping and install screenshots.
Does Route Receipts store customer payment data on its servers? 🔒
Route Receipts stores only the minimal Stripe-derived fields required to evaluate and record receipt-routing decisions and does not store full card numbers or raw payment instrument data. Our privacy policy explains which fields we persist, how long we retain them, and which third-party processors we use; refer to Route Receipts privacy policy for retention timelines and processor details. For security reviews, request an exported data inventory from our support team that lists the exact fields tied to your Stripe account ID. If you need further evidence for a vendor security questionnaire, our Support team can supply the export and processing notes.
How does Route Receipts support GDPR data subject requests? 📁
Route Receipts supports data subject requests by locating account-scoped records it processes and providing exports or deletions per the procedures in our privacy policy. To request an export or deletion, the Stripe account owner submits a ticket via our support channel with the Stripe account ID and request scope; our documentation outlines the required information and expected turnaround. For internal workflows, document the date you requested the export, attach the Route Receipts audit export, and reconcile it with Stripe account exports to show a complete data trail. See our privacy policy for details on retention and the types of records we return for a subject access request, and contact Support to start a request.
Can I install Route Receipts with least-privilege scopes only? ✅
Yes. Route Receipts supports minimal-scope installs and documents the smallest set of permissions required for core receipt routing. We recommend testing a least-privilege install in a Stripe test account to verify behavior before enabling in production, then expanding scopes only if a specific feature requires them. The typical checklist for a least-privilege install: 1) install into a sandbox Stripe account and confirm the allowlist UI functions; 2) run a set of sample invoices to validate routing decisions and decision-log entries; 3) export the Route Receipts decision log and the Stripe installed-scope listing to confirm no extra permissions were granted. Follow the step-by-step install flow in our Documentation or read the beginner's setup in our blog post, "The No‑Code Way to Route Customer Receipts in Stripe."
💡 Tip: Test the minimal-scope install in a sandbox account and run at least 20 sample invoices that cover invoice, charge, and customer-update events before moving to production.
What audit logs does Route Receipts provide for security reviews? 📝
Route Receipts provides an exportable decision audit log that records allowlist changes, operator identity, timestamps, and each routing decision. That decision log includes who made the change (dashboard user or API key), why the decision was made when available, and whether the action came from an operator or an automated rule. For SOC 2 evidence, combine the Route Receipts decision log with Stripe's installed-scope listing to show both access and resulting actions; this pairing satisfies common SOC 2 controls for Stripe apps that require traceable access-to-action mapping. Our documentation explains how to export the decision log and the recommended fields to include in an audit package; contact Support if you need a formatted export for compliance archives.
How does Route Receipts behave with Stripe Connect and multiple accounts? 🔗
Route Receipts requests consent and scopes on a per-connected-account basis and enforces per-account isolation for routing decisions. For platforms using Stripe Connect, each connected account must grant the required scopes during installation; Route Receipts stores decisions linked to the specific connected account ID so routing and audit trails remain isolated. For governance across many accounts, collect each connected account's installed-scope listing and aggregate Route Receipts decision logs for a centralized compliance review. If you use entitlement controls, treat account-scoped versus object-scoped permissions differently: account-scoped grants allow Route Receipts to access all account objects, while object-scoped grants limit access to particular customer or invoice records; our Documentation explains how to interpret those distinctions and suggests a post-install audit and revocation workflow.
For quick references and common install questions, see our Frequently Asked Questions and the article "Why Did We Build Route Receipts?" for context on design choices and auditability.
Next steps: verify permissions, audit logs, and request compliance evidence.
RouteReceipts reduces procurement friction by making app scopes, data flows, and audit trails easy to review. According to our documentation, RouteReceipts Stripe app permissions and scopes are scoped to invoice and customer data needed to make routing decisions, while audit logs record each routing decision for evidence. For context, RouteReceipts is a specialized application that enhances the way businesses manage their Stripe receipt distribution. This app addresses a significant limitation within Stripe's native functionality, which traditionally forces businesses to either send receipts to all customers or none at all. RouteReceipts empowers businesses with the flexibility to selectively send receipts to specific customers, thereby preventing unnecessary email clutter for those who do not require them. By integrating directly into the Stripe dashboard, RouteReceipts allows users to manage an allowlist of customers effortlessly, without the need for complex coding or custom webhook integrations.
Contact our team via the support page to request SOC 2 artifact summaries or specific audit evidence and to discuss deployment for your account. See the FAQ for install questions and the setup guide for step-by-step configuration: FAQ, Documentation, Support.
💡 Tip: When you reach out, include your Stripe account ID and a few example receipt IDs to speed evidence delivery.
